How a Reddit rumour became a National News story, how likely is malware in your e-cig, and how to stop it from ever happening
Imagine this.
Your new e-cig comes in. You immediately plug the battery into your laptop to start charging it.
Unknown to you, a small piece of software crawls into your computer, installs itself and starts collecting and uploading your personal information, passwords and credit card information - or even disabling your PC.
Sound alarming?
According to numerous newspaper reports, that's exactly what happened. But search online, and you'll soon find there are no reputable sources for this story.
In fact in most of our own e-cigarette USB chargers, there are no data cables inside, meaning it would be impossible for them to spread a virus. (That doesn't mean there aren't other e-cigarette chargers with data cables out there, of course!)The Research the Papers Didn't Do
We've been cutting up USB cables and taking apart USB plugs, talking to the industry and contacting virus experts. We've also tried to contact the person who started it all off.Here's what we found out.How the Story Came About
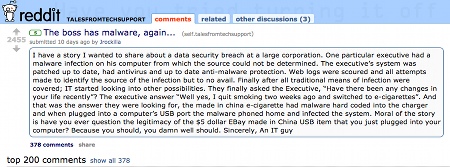
Here's what happened.1. Claim: A person on Reddit pastes a story of someone who claims their boss had a virus from e-cigs.
Click on the image for a larger picture, or here to view the thread on Reddit:
2. Rumour: The Guardian picks it up, but is careful to use the words 'can potentially'.
3. Fact: Once the Guardian has reported the rumour, it gains credibility, and becomes fact, with other titles become ever more extreme:
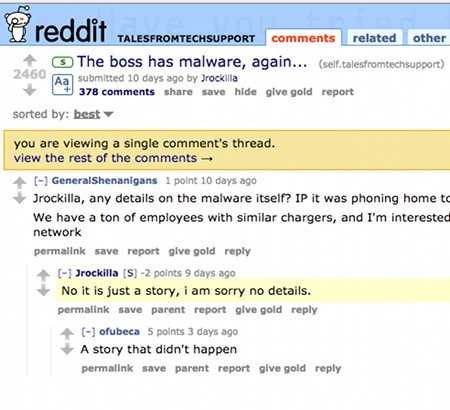
Pretty strong headlines, especially considering the fact that the sources of the claims, Jrockilla, said that it was 'just a story':
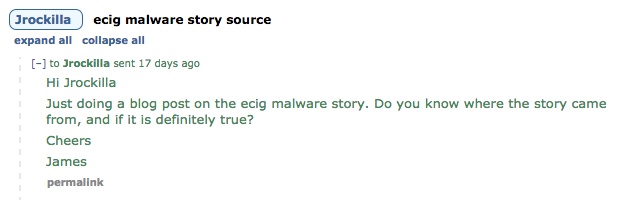
I messaged Jrockilla on Reddit to query the source of the story:
At the time of writing I haven't had a reply, although to be fair I don't know if Jrockilla checks his Reddit messages, or if he is just sick of the whole story.What the Experts Say
Vicky from ECITA has worked with dozens of electronic cigarette companies, and has never heard of a USB charger passing malware or a virus. She told us:[It]...just seems, well a bit far-fetched.John Hawes, chief operator of Virus Bulletin and Sophos blogger, agreed, telling us:Although not impossible, it seems very implausible and had this truly been the case then we would have expected to see many reports of malware being transferred to PC's and laptops all over the world, not just one instance of it.
As far as we’re aware there hasn’t been any actual evidence of malware riding in on e-cigarettes, chargers/adaptors or anything related – the whole story was based on an anecdote posted on Reddit with very little detail to back it up.It's a fascinating example of how news works today, a process highlighted in Ryan Haliday's book, Confessions of a Media Manipulator and Liar:
The link economy encourages bloggers to repeat what “other people are saying” and link to it instead of doing their own reporting and standing behind it. This changes the news from what has happened into what someone said the news is.It's also a reminder never to trust what you read on the net (unless it's on the Ashtray Blog, of course! ;) )(By the way, I am not saying there's no way it could have happened - just that a post on Reddit is hardly a sufficient source for a National News story!)
Is It Possible?
It could be, if your USB device uses data points and data cables. If you're technically minded, you can even find instructions online for you to make your own malicious USB device.When you plug in your USB device, the USB controller tells your computer what type of device it is and what drivers it needs to work correctly. Experts at security conferences have shown that a USB controller can be exploited to run malicious code when attached to your computer, however, this would be quite expensive and require more effort than sending a few million spam emails.
All of the charger cables we cut up while researching this blog post did not have data cables, so could not carry a virus. This means that only power can flow from the host (your computer or wall plug) to your device.
Bottom line; even if it is possible, according to John Hawes the task is likely to be both difficult and relatively unrewarding.
From a technical point of view it’s not entirely impossible. Someone could feasibly (just about) doctor an adaptor (or battery in the case of those which but just have a micro-USB socket on them) and pre-load it with malware, but given the size of most of them it would be quite a task, and the returns would be minimal.John went on to explain that from a return on investment point of view, it would be cheaper, easier and more effective to stick to sending viruses by email.We've also talked to battery suppliers in China, who denied that it could ever happen to their devices in the manufacturing process, although to be fair they're not exactly likely to admit it if it had happened.
6 Ways to Stop You E-Cig From Getting A Virus
1. Use a USB condom. This is an innovative device that grew from a KickStarter project.2. Use a wall plug instead of your computer or laptop. In fact, John Hawes recommends banning the use of USB ports in a business setting, or even disabling them. You can also disable the data access parts of your USB cables, allowing charging to continue without allowing data to be transferred.
3. When you plug your USB into your computer, look at the information provided - is it purely providing charge or is it also providing data access? But bear in mind that if someone had altered your data USB cable, it is not beyond the realms of possibility for malware creators to 'trick' the computer.
4. Dig into the charger/battery and check if the data pins on the USB are linked to data cables (John believes this is unlikely).
5. Buy from a reputable retailer. As mentioned above, we've contacted ECITA and they have never known an ECITA member to have this problem.
6. Don’t access your computer with an admin/super-user account for day to day use. This makes it much harder for any malicious application to run. Click here for Microsoft's comment on using a standard user in Windows.
Do you think the virus story was a hoax? Let us know in the comments!